TravelOps
Validation status:
CI status:
Links:
About the travelops pattern
- Use case
Use a GitOps approach to manage hybrid and multi-cloud deployments across both public and private clouds.
Enable cross-cluster governance and application lifecycle management.
Securely manage secrets across the deployment.
Based on the requirements of a specific implementation, certain details might differ. However, all validated patterns that are based on a portfolio architecture, generalize one or more successful deployments of a use case.
- Background
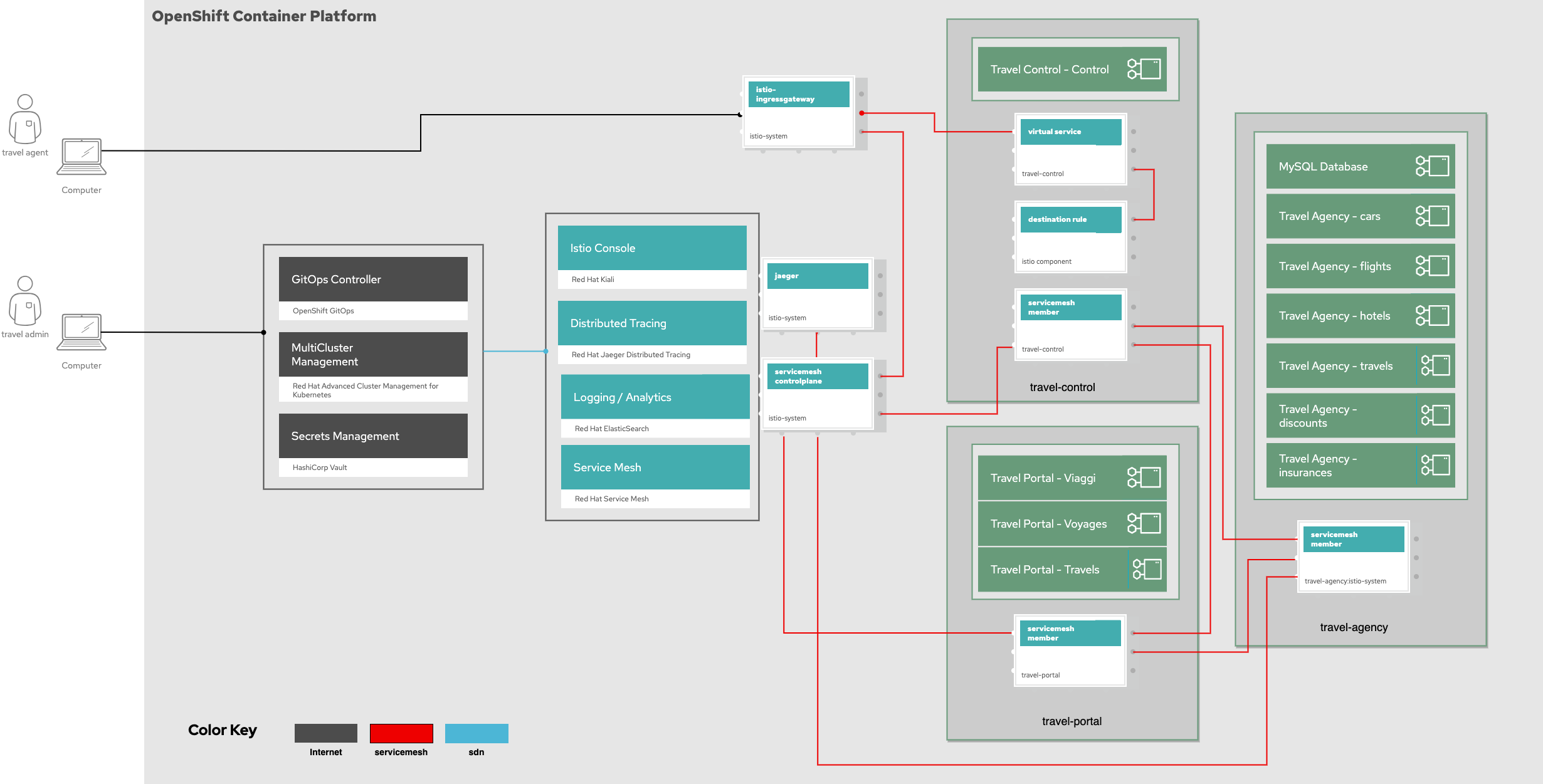
The TravelOps pattern deployed using OpenShift GitOps and is comprised of Red Hat Service Mesh (RHSM), Kiali for the Service Mesh console, Jaeger for distributed tracing, and elasticsearch for logging and analytics. The application deployed is from the Kiali traveldemo. This pattern focuses on demonstrating capabilities enabled through simple configurations, rather than the demo itself. Service Mesh technology is adopted across multiple platforms to ensure secure communication between services.
Organizations are aiming to develop, deploy, and operate applications on an open hybrid cloud in a stable, simple, and secure way. This hybrid strategy includes multi-cloud deployments where workloads might be running on multiple clusters and on multiple clouds, private or public. This strategy requires an infrastructure-as-code approach: GitOps. GitOps uses Git repositories as a single source of truth to deliver infrastructure-as-code. Submitted code will be checked by the continuous integration (CI) process, while the continuous delivery (CD) process checks and applies requirements for things like security, infrastructure-as-code, or any other boundaries set for the application framework. All changes to code are tracked, making updates easy while also providing version control should a rollback be needed.
About the solution
This architecture covers a single cluster for all DevOps and GitOps functionality. However, one could extend this architecture to meet hybrid or multicloud demand using a GitOps approach
Benefits of Hybrid Multicloud management with GitOps:
Unify management across cloud environments.
Dynamic infrastructure security.
Infrastructural continuous delivery best practices.
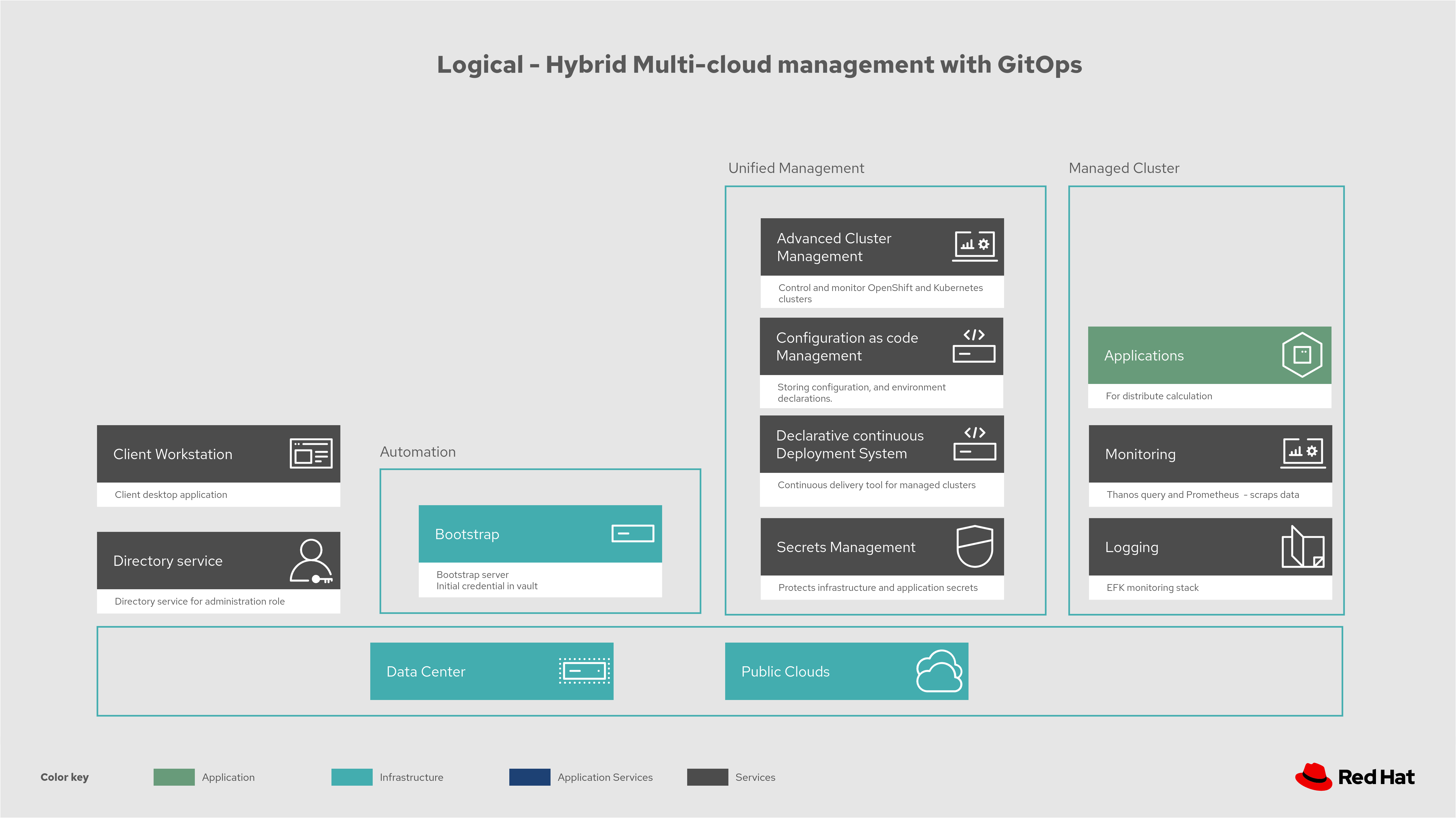
In the following figure, logically, this solution can be viewed as being composed of an automation component, unified management including secrets management, and the clusters under management, all running on top of a user-chosen mixture of on-premise data centers and public clouds.
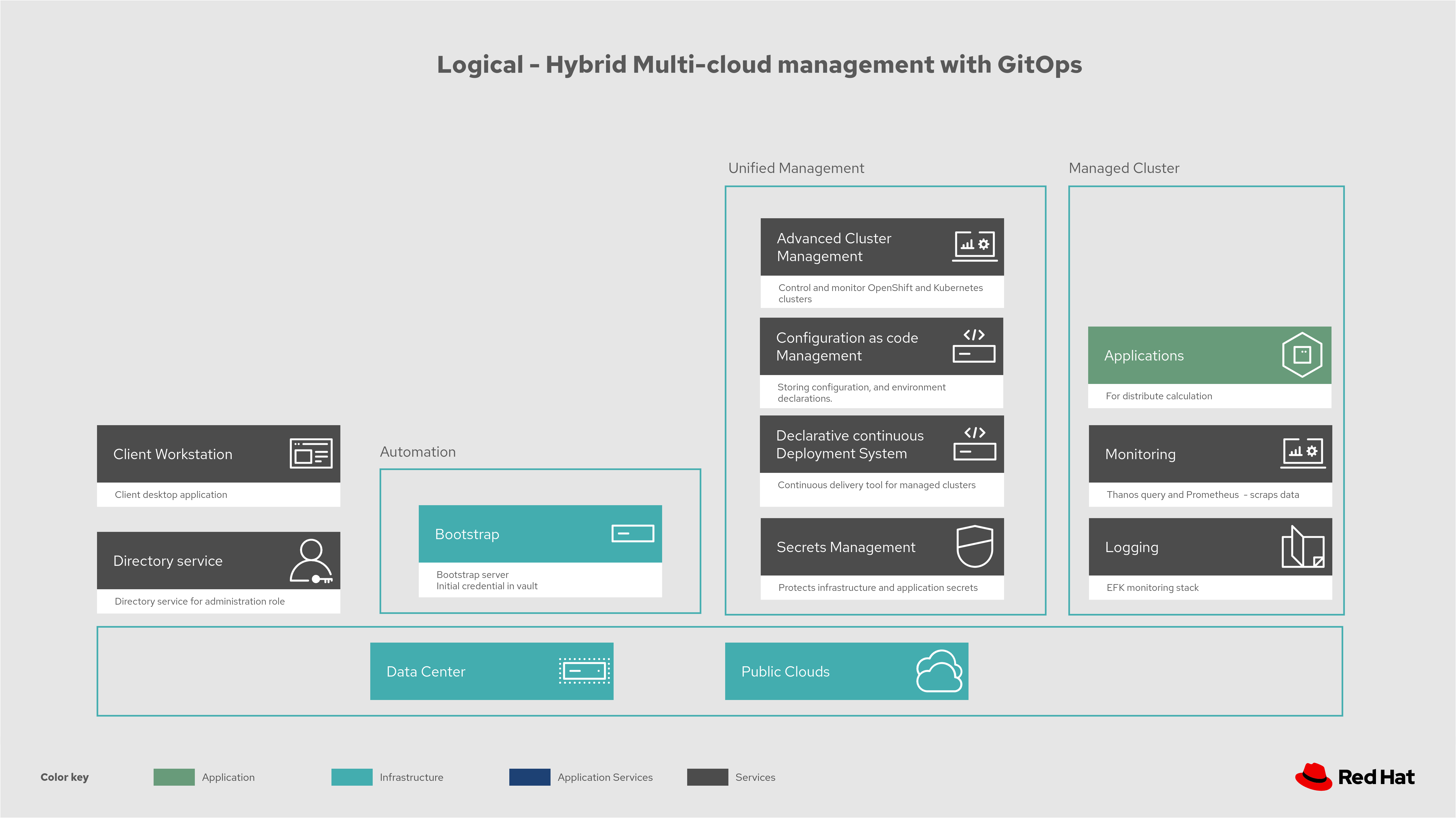
Figure 1. Logical diagram of hybrid multi-cloud management with GitOps
About the technology
The following technologies are used in this solution:
- Red Hat OpenShift Platform
An enterprise-ready Kubernetes container platform built for an open hybrid cloud strategy. It provides a consistent application platform to manage hybrid cloud, public cloud, and edge deployments. It delivers a complete application platform for both traditional and cloud-native applications, allowing them to run anywhere. OpenShift has a pre-configured, pre-installed, and self-updating monitoring stack that provides monitoring for core platform components. It also enables the use of external secret management systems, for example, HashiCorp Vault in this case, to securely add secrets into the OpenShift platform.
- Red Hat OpenShift GitOps
A declarative application continuous delivery tool for Kubernetes based on the ArgoCD project. Application definitions, configurations, and environments are declarative and version controlled in Git. It can automatically push the desired application state into a cluster, quickly find out if the application state is in sync with the desired state, and manage applications in multi-cluster environments.
- Red Hat Advanced Cluster Management for Kubernetes
Controls clusters and applications from a single console, with built-in security policies. Extends the value of Red Hat OpenShift by deploying apps, managing multiple clusters, and enforcing policies across multiple clusters at scale.
- Red Hat Service Mesh
Red Hat® OpenShift Service Mesh provides a uniform way to connect, manage, and observe microservices-based applications.
- Red Hat Ansible Automation Platform
Provides an enterprise framework for building and operating IT automation at scale across hybrid clouds including edge deployments. It enables users across an organization to create, share, and manage automation, from development and operations to security and network teams.
- Hashicorp Vault
Provides a secure centralized store for dynamic infrastructure and applications across clusters, including over low-trust networks between clouds and data centers.
This solution also uses a variety of observability tools including the Prometheus monitoring and Grafana dashboard that are integrated with OpenShift as well as components of the Observatorium meta-project which includes Thanos and the Loki API.
Overview of the architectures
The following figure provides a high level architectural overview of the travelops pattern.
Subsequent schematic diagrams provide details on:
Hybrid multi-cloud GitOps
Dynamic security management
Hybrid Multicloud GitOps
The following figure provides a schematic diagram showing remaining activities associated with setting up the management hub and clusters using Red Hat Advanced Cluster Management.
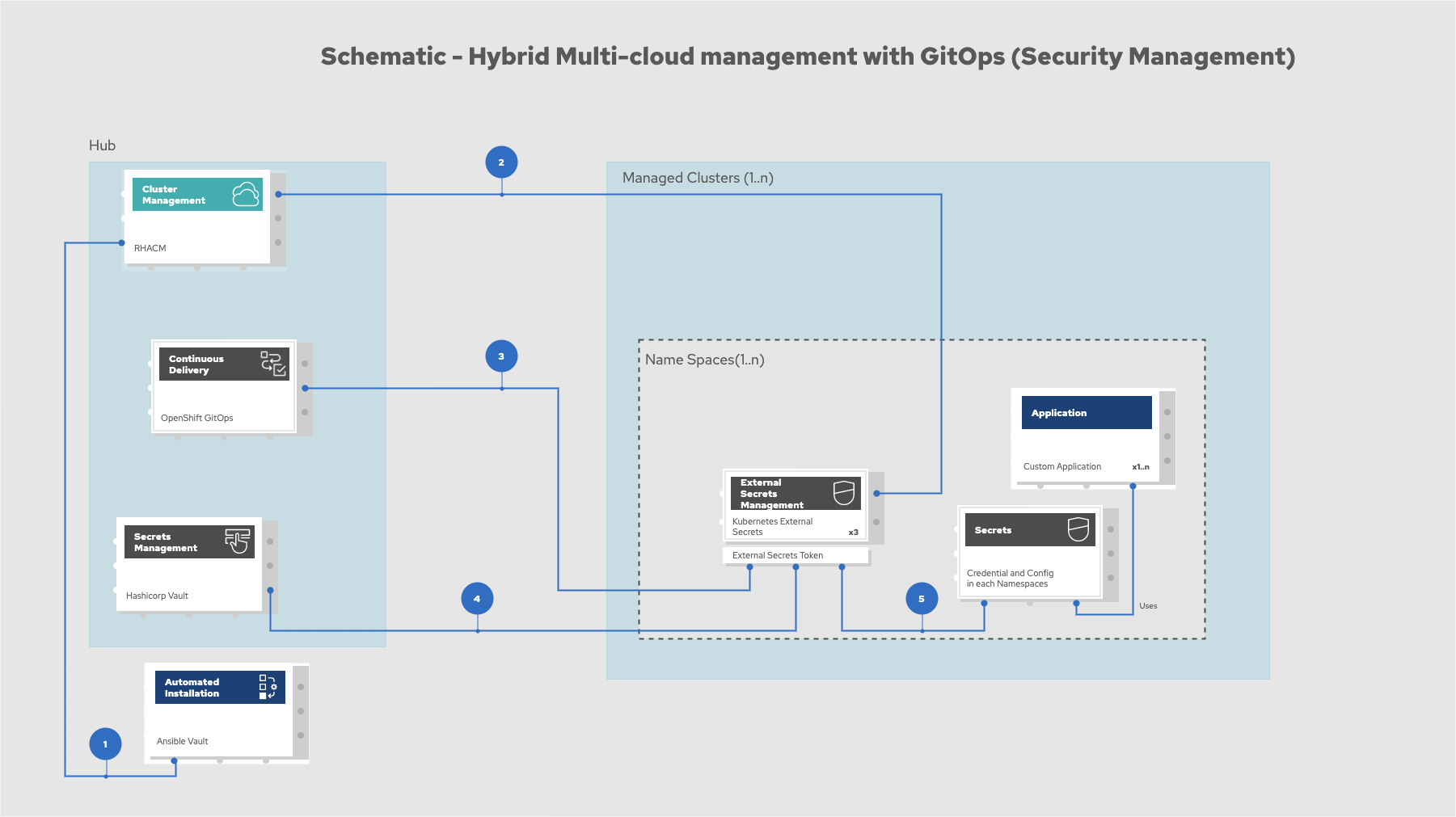
Figure 3. Schematic diagram of hybrid multi-cloud management with GitOps
Manifest and configuration are set as code template in the form of a
KustomizationYAML file. The file describes the desired end state of the managed cluster. When complete, theKustomizationYAML file is pushed into the source control management repository with a version assigned to each update.OpenShift GitOps monitors the repository and detects changes in the repository.
OpenShift GitOps creates and updates the manifest by creating Kubernetes objects on top of Red Hat Advanced Cluster Management.
Red Hat Advanced Cluster Management provisions, updates, or deletes managed clusters and configuration according to the manifest. In the manifest, you can configure what cloud provider the cluster will be on, the name of the cluster, infrastructure node details and worker node. Governance policy can also be applied as well as provision an agent in the cluster as the bridge between the control center and the managed cluster.
OpenShift GitOps continuously monitors the code repository and the status of the clusters reported back to Red Hat Advanced Cluster Management. Any configuration drift or in case of any failure, OpenShift GitOps will automatically try to remediate by applying the manifest or by displaying alerts for manual intervention.
Dynamic security management
The following figure provides a schematic diagram showing how secrets are handled in this solution.
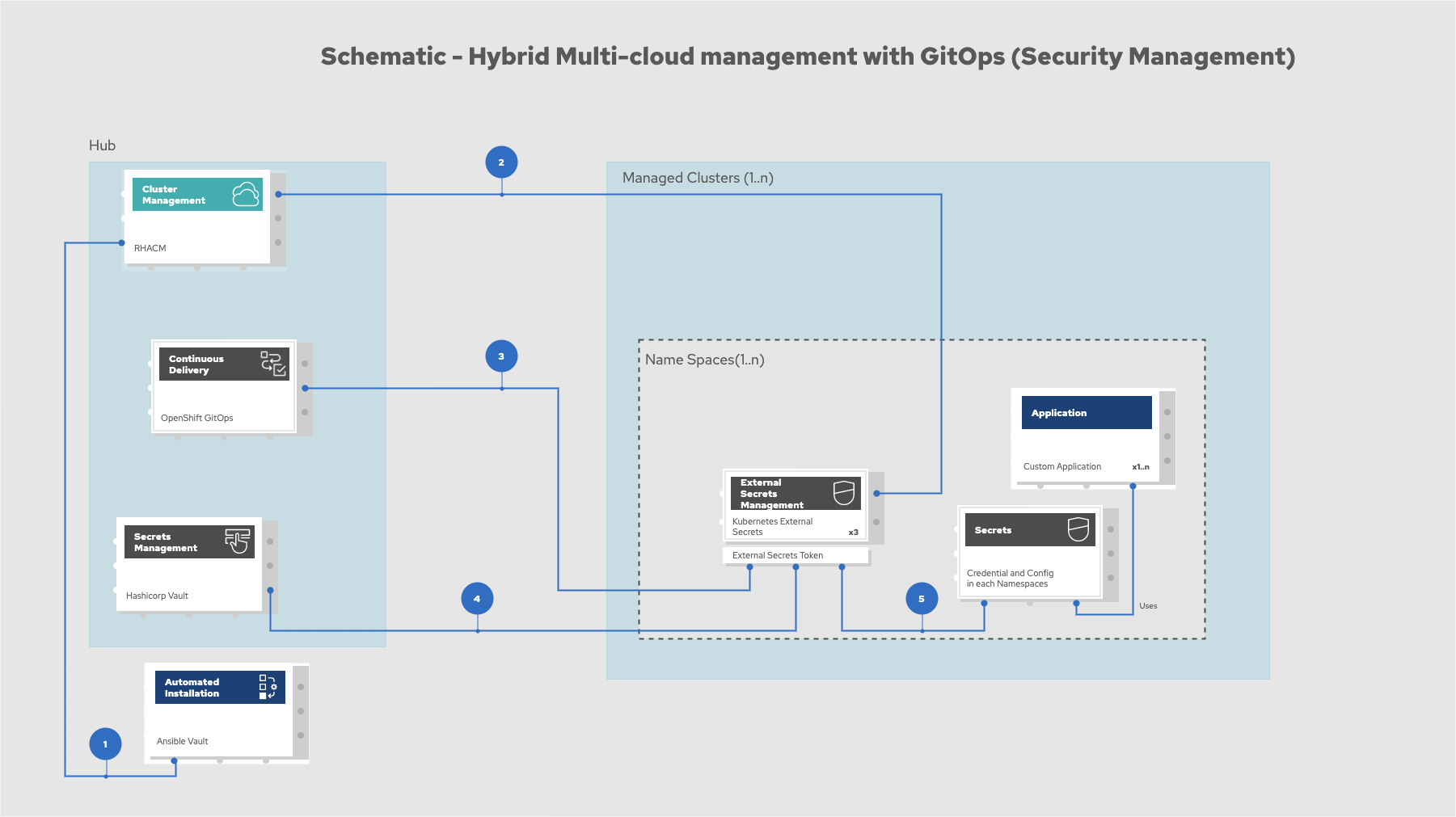
Figure 4. Schematic showing the setup and use of external secrets management
During setup, the token to securely access HashiCorp Vault is stored in Ansible Vault. It is encrypted to protect sensitive content.
Red Hat Advanced Cluster Management for Kubernetes acquires the token from Ansible Vault during install and distributes it among the clusters. As a result, you have centralized control over the managed clusters through RHACM.
To allow the cluster access to the external vault, you must set up the external secret management with Helm in this study. OpenShift Gitops is used to deploy the external secret object to a managed cluster.
External secret management fetches secrets from HashiCorp Vault by using the token that was generated in step 2 and constantly monitors for updates.
Secrets are created in each namespace, where applications can use them.